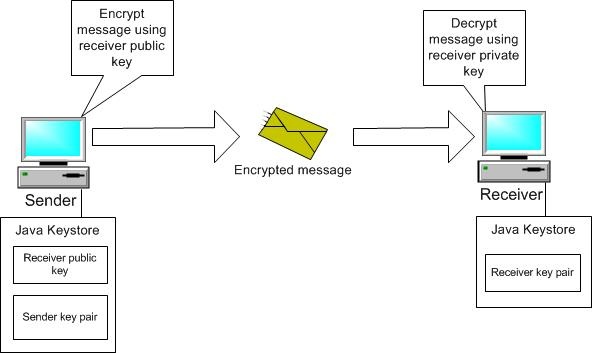
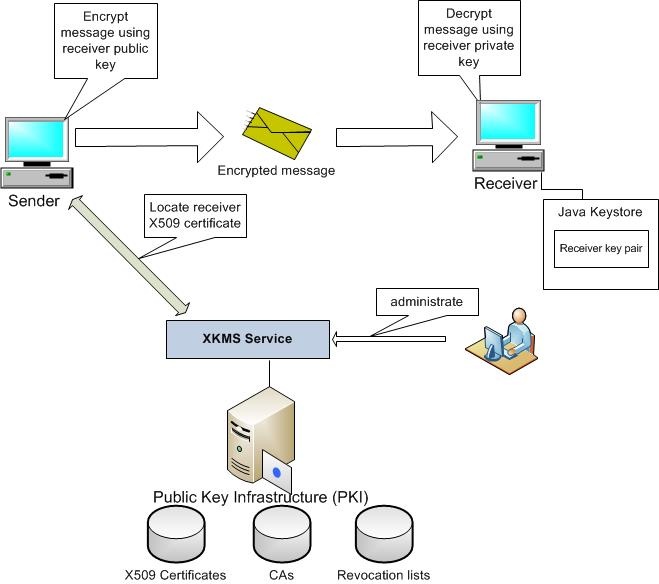
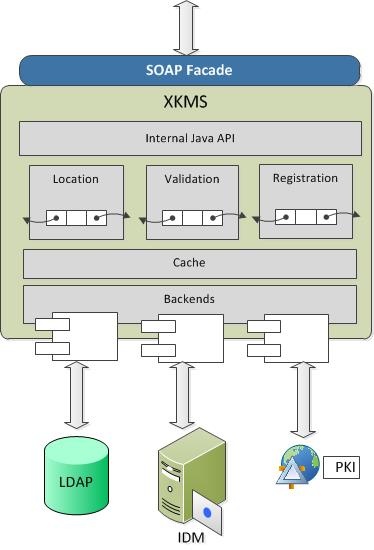
XML Key Management Service (XKMS)Available since CXF 2.7.7. Use caseCXF uses asymmetric algorithms for different purposes: encryption of symmetric keys and payloads, signing security tokens and messages, proof of possession, etc. For example, if the sender encrypts the message payload sending to the receiver, he should have access to the receiver certificate saved in the local keystore. Seems to be OK? Imagine now that you have a production environment with 100 different clients of this service and the service certificate is expired. You should reissue and replace the certificate in ALL client keystores! Even more, if keystores are packaged into war files or OSGi bundles – they should be unpackaged and updated. Not really acceptable for enterprise environments. Therefore large service landscapes support central certificates management. It means that X509 certificates are not stored locally in keystores, but are provided and administrated centrally. Normally it is a responsibility of Public Key Infrastructure (PKI) established in the organization. PKI is responsible to create, manage, store, distribute, synchronize and revoke public certificates and certification authorities (CAs). XKMS SpecificationW3C specifies a protocol to distribute and register public keys, certificates and CAs that can be used for XML-based cryptography, including signature and encryption: XML Key Management Specification (XKMS 2.0). The XKMS SOAP interface can be used as a standard frontend to access the Public Key Infrastructure (PKI). Using XKMS message encryption scenario, the message encryption picture will change in the following way: Receiver X509 certificate is not saved into sender's local keystore anymore. Instead, certificate is stored into central PKI and can be located, validated and administrated using standard XKMS interface. This essentially improves the control on certificates in large services landscape. Administrator can update, renew and revoke certificates, manage certification authorities and revocation lists. Integrating the XKMS client into the CXF runtimeThe XKMS client can be integrated into CXF and WSS4J in pretty elegant way using a custom Crypto provider implementation. In this case, the XKMS service will be automatically invoked when WSS4J asks for the certificates or validates them. Details are described in this blog. A basic XKMS implementation of WSS4J Crypto interface is available in XKMS Client component (XKMSCryptoProvider and XKMSCryptoProviderFactory). Implementation uses Ehcache to cache certificates received from XKMS service. XKMS Service DesignInternal structure of XKMS service is represented in the following figure: The XKMS Service exposes a SOAP interface specified in XKMS 2.0. Currently the XKMS Service supports simple file based and LDAP backends. <beans xmlns="http://www.springframework.org/schema/beans"
xmlns:cxf="http://cxf.apache.org/core" xmlns:jaxws="http://cxf.apache.org/jaxws"
xmlns:test="http://apache.org/hello_world_soap_http" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:util="http://www.springframework.org/schema/util"
xsi:schemaLocation="
http://cxf.apache.org/core
http://cxf.apache.org/schemas/core.xsd
http://www.springframework.org/schema/beans
http://www.springframework.org/schema/beans/spring-beans-2.0.xsd
http://cxf.apache.org/jaxws
http://cxf.apache.org/schemas/jaxws.xsd
http://www.springframework.org/schema/util
http://www.springframework.org/schema/util/spring-util-2.0.xsd">
<bean id="dateValidator" class="org.apache.cxf.xkms.x509.validator.DateValidator" />
<bean id="trustedAuthorityValidator"
class="org.apache.cxf.xkms.x509.validator.TrustedAuthorityValidator">
<constructor-arg ref="certificateRepo" />
</bean>
<bean id="x509Locator" class="org.apache.cxf.xkms.x509.handlers.X509Locator">
<constructor-arg ref="certificateRepo" />
</bean>
<bean id="x509Register"
class="org.apache.cxf.xkms.x509.handlers.x509Register">
<constructor-arg ref="certificateRepo" />
</bean>
<!-- LDAP based implementation -->
<bean id="certificateRepo"
class="org.apache.cxf.xkms.x509.repo.ldap.LdapCertificateRepo">
<constructor-arg ref="ldapSearch" />
<constructor-arg ref="ldapSchemaConfig" />
<constructor-arg value="dc=example,dc=com" />
</bean>
<bean id="ldapSearch" class="org.apache.cxf.xkms.x509.repo.ldap.LdapSearch">
<constructor-arg value="ldap://localhost:2389" />
<constructor-arg value="cn=Directory Manager,dc=example,dc=com" />
<constructor-arg value="test" />
<constructor-arg value="2" />
</bean>
<bean id="ldapSchemaConfig" class="org.apache.cxf.xkms.x509.repo.ldap.LdapSchemaConfig">
<property name="certObjectClass" value="inetOrgPerson" />
<property name="attrUID" value="uid" />
<property name="attrIssuerID" value="manager" />
<property name="attrSerialNumber" value="employeeNumber" />
<property name="attrCrtBinary" value="userCertificate;binary" />
<property name="constAttrNamesCSV" value="sn" />
<property name="constAttrValuesCSV" value="X509 certificate" />
<property name="serviceCertRDNTemplate" value="cn=%s,ou=services" />
<property name="serviceCertUIDTemplate" value="cn=%s" />
<property name="trustedAuthorityFilter" value="(&(objectClass=inetOrgPerson)(ou:dn:=CAs))" />
<property name="intermediateFilter" value="(objectClass=inetOrgPerson)" />
</bean>
<!-- File based implementation -->
<!-- bean id="certificateRepo"
class="org.apache.cxf.xkms.x509.repo.file.FileCertificateRepo">
<constructor-arg value="../conf/certs" />
</bean-->
</beans>
The dateValidator and trustedAuthorityValidator beans are implementations of the Validator interface for date and trusted chain validation.
Supported certificates types.XKMS distinguishes between the following types of X509 certificates:
XKMS service endpoint is configured in the following way: <bean id="xkmsProviderBean" class="org.apache.cxf.xkms.service.XKMSService">
<property name="validators">
<list>
<ref bean="dateValidator" />
<ref bean="trustedAuthorityValidator" />
</list>
</property>
<property name="locators">
<list>
<ref bean="x509Locator" />
</list>
</property>
<property name="keyRegisterHandlers">
<list>
<ref bean="x509Register" />
</list>
</property>
</bean>
<jaxws:endpoint id="XKMSService"
xmlns:serviceNamespace="http://www.w3.org/2002/03/xkms#wsdl"
serviceName="serviceNamespace:XKMSService" endpointName="serviceNamespace:XKMSPort"
implementor="#xkmsProviderBean" address="/XKMS">
</jaxws:endpoint>
Data FormatsInput and output data formats are specified in XML Key Management Service Specification Version 2.0 (see XKMS 2.0). The XKMS service supports only a subset of the specified requests and responses.
Error HandlingSuccess and Fault Response formats are specified in XKMS 2.0. Error conditions in XKMS service are reported using ResultMajor and ResultMinor attributes in the root response element. ResultMajor
ResultMinor
DeploymentThe XKMS Service can be deployed into web and OSGi containers. The Service implementation was tested with Tomcat and Karaf. Sample Requests and ResponsesSample request for Locate operation: <soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/">
<soap:Body>
<ns2:LocateRequest xmlns="http://www.w3.org/2000/09/xmldsig#"
xmlns:ns2="http://www.w3.org/2002/03/xkms#"
xmlns:ns3="http://www.w3.org/2001/04/xmlenc#"
Id="I047257513d19456687e6b4f4a2a72606" Service="http://cxf.apache.org/services/XKMS/">
<ns2:QueryKeyBinding>
<ns2:UseKeyWith Application="urn:ietf:rfc:2459"
Identifier="EMAILADDRESS=client@client.com, CN=www.client.com, OU=IT Department,
O=Sample Client -- NOT FOR PRODUCTION, L=Niagara Falls, ST=New York, C=US" />
</ns2:QueryKeyBinding>
</ns2:LocateRequest>
</soap:Body>
</soap:Envelope>
Sample response for Locate operation: <soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/">
<soap:Body>
<ns2:LocateResult ResultMajor="http://www.w3.org/2002/03/xkms#Success"
RequestId="I047257513d19456687e6b4f4a2a72606" Id="I0758390284847918129574923948"
Service="http://cxf.apache.org/services/XKMS/"
xmlns:ns2="http://www.w3.org/2002/03/xkms#"
xmlns:ns3="http://www.w3.org/2001/04/xmlenc#"
xmlns:ns4="http://www.w3.org/2000/09/xmldsig#"
xmlns:ns5="http://www.w3.org/2002/03/xkms#wsdl">
<ns2:UnverifiedKeyBinding>
<ns4:KeyInfo>
<ns4:X509Data>
<ns4:X509Certificate>… </ns4:X509Certificate>
</ns4:X509Data>
</ns4:KeyInfo>
</ns2:UnverifiedKeyBinding>
</ns2:LocateResult>
</soap:Body>
</soap:Envelope>
Sample error message: <soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/">
<soap:Body>
<ns2:LocateResult ResultMajor="http://www.w3.org/2002/03/xkms#Receiver"
ResultMinor="http://www.w3.org/2002/03/xkms#Failure"
RequestId="I047257513d19456687e6b4f4a2a72606" Id="I0758390284847918129574923948"
Service="http://cxf.apache.org/services/XKMS/"
xmlns:ns2="http://www.w3.org/2002/03/xkms#"
xmlns:ns3="http://www.w3.org/2001/04/xmlenc#"
xmlns:ns4="http://www.w3.org/2000/09/xmldsig#"
xmlns:ns5="http://www.w3.org/2002/03/xkms#wsdl">
<ns2:MessageExtension xsi:type="ns5:resultDetails"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance">
<Details>Search certificates failure: Application
identifier not supported</Details>
</ns2:MessageExtension>
</ns2:LocateResult>
</soap:Body>
</soap:Envelope>
Current restrictions and ToDos
|